Server-less internet censorship circumvention that does not use third-party servers and does not affect the internet connection speed.
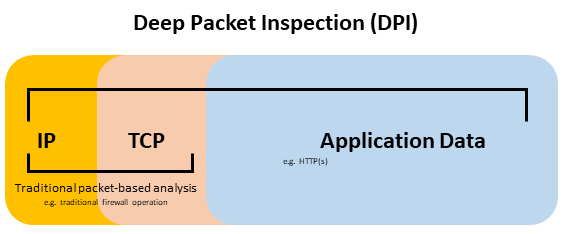
No secret that many enterprises, service providers and governments do implement Deep Packet Inspection (DPI) solutions to filter-out blacklisted contents and or address other cybersecurity concerns. Many might come across access restrictions to certain web sites and other contents. It can be adult content in Middle Eastern countries, foreign entertainment giants in China or torrent sites in Russia.
According to Market Research Future (MRFR) research report, the global DPI market has been figured to be worth the USD 19 bn by the end of 2023. Back in 2013, it was estimated just around USD 1 bn.
Apparently, there is no uniform standard that drives the solution development. Vendors follow different techniques and implementation types.
There are two ways DPI is implemented (i) Active DPI (ii) Passive DPI.
Active DPI – the solution is put in-line with traffic path and desired traffic can be dropped/reset as it flows. Typically configured to inspect only egress HTTP(s) headers directed to the specific IP subnet. This is required to achieve a higher cost to performance ratios.
Passive DPI – out-of-path snooping, where HTTP redirect message (code 302) or TCP reset (typically with Identification = 1, Flags = 0, Fragment Offset = 0, 0x60 = «warn» ) sent to the client. The solution is typically more economically viable for corporate and service providers and does not impact overall network performance.
Above deployment, limitations can be exploited by one to overcome DPI filtering. For instance, in the case of Active DPI implementation, one may decide to construct HTTP(s) header using permissible, but unparsable options available in RFC 7230 (newer standard, released in 2014) or RFC 2616 (released back in 1999). To illustrate an example, DPI may be configured to parse header to match “Host:” followed by the website hostname, whereas RFC permits sending “hoSt:” or even “Host :” (note the extra space). Depending on the DPI configuration, such traffic may slip through unchecked.
Similarly in case of Passive DPI, one may decide to force the operating system to ignore TCP reset packets containing sequence of Identification = 1, Flags = 0, Fragment Offset = 0, 0x60 = «warn».
Interestingly enough, recently I came across GitHub with open source binaries and source code of the DPI deception solution for Windows. The collection is called GoodbyeDPI well maintained and frequently updated by the author ValdikSS.
It appears that the method works in a number of countries including Russia, China and some in MENA.


